 SOLUTION
SOLUTION
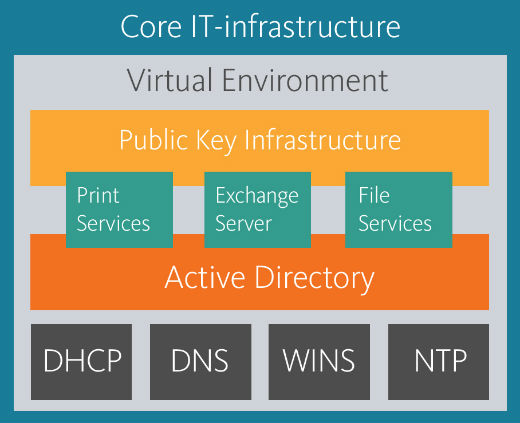
This solution is so called “start package” required for creating IT-infrastructure based on Microsoft technologies and products almost in every company. This “package” includes a set of services required for IT-infrastructure working start and further development. All solution components are interconnected and as a unit provide the basis for IT-infrastructure further growth.
Network services
- DHCP – deals with automatic configuring network parameters and management of IP-addresses allocation in local network.
- DNS – allows creating and managing network nodes names hierarchy simplifying search and making access to network resources faster.
- NTP – is used by computers and services for time synchronization with a source of accurate time. It is necessary for correct work of user authentication and authorization processes.
- WINS – is an optional component providing short network node names resolution. However it is required to be included to the infrastructure for a lot of Microsoft products work, e.g. for mail server based on Microsoft Exchange Server 2013.
Network services are also required for Active Directory work. This service is necessary for creating domain structure in the IT-infrastructure of your company, due to which your IT-infrastructure gains a lot of useful possibilities:
- Authentication – the process verifying the identity of a user logging in to the system. The user that does not have “digital ID” in the domain cannot access your IT-infrastructure. The additional advantage of Active Directory is its possibility to be integrated with authentication services of external developers supporting Kerberos authentication protocol.
- Authorization – process of granting a user access to an IT-resource of the company according to specified rules.
- Single Sign-On – technology allowing user access to different domain IT-resources using single “digital ID”.
- Group Policy – technology of centralized management of Microsoft operating systems parameters (security settings, services, network parameters, roles, etc.), access to applications and user environment (desktop, appearance settings, accessories, access to drivers, files and directories).
- Centralized objects control – allows easy creating, deleting and editing objects of domain structure (users, computers, groups, printers) located in different geographic regions. It also gives you possibility to group them basing on their similar properties and features (geographic location, administrative privileges, etc.) from single administrative location.
- Address book – allows secure storing and editing detailed user information that can be used in various Microsoft products. For instance, address book is used by mail system Microsoft Exchange Server and other software concerning Unified Communications Technology.
Besides Active Directory stores data of authentication, enterprise network physical structure and domain structure. Working of many other Microsoft products, automating system administration processes and further developing company IT-infrastructure require these data.
Using Active Directory gives you possibility to work with additional useful services:
- Active Directory Rights Management Service is used to protect document workflow and E-mail messages inside the company.
- Active Directory Federation Services – allows granting your business partners or external organizations access to selected IT-resources of your company.
- Active Directory Lightweight Directory Service – allows creating LDAP-compatible databases for storing information necessary for work of business-line applications of your company when required.
Furthermore Active Directory significantly expands possibilities of Certificate Management System (Certification Authority) required to implement Public-Key Infrastructure (PKI) in the company and to use digital certificates and smart cards to enhance security of access to data.
Almost every contemporary company implements services for E-mail messages exchange. Our “start package” includes Microsoft Exchange Server 2013 that can allow your employees to begin using E-mail as soon as possible. Exchange Server 2013 has a lot of advantages:
- It can be easily and quickly deployed within the infrastructure with the help of installation wizard, which is user-friendly and automated to the great extent.
- It automatically scans all incoming and outgoing messages for potentially malicious objects or spam.
- It provides users with secure access to mail boxes when being located outside the office and using mobile devices.
- It can be integrated with various additional Microsoft services, e.g. Bing maps.
When you use Active Directory and Windows Server 2012 operating system, functionality of Print Service and File services expands to great extent – access to files and printers can be adjusted not only basing on user groups but using Dynamic Access Control rules, which simplify administrative part in managing users access rights. Files and folders now can be classified by tagging and access can be centrally managed using policies of access to classified files. Using special tools included into File services you can create and edit disk quotas for users, perform screening of file resources to prevent downloading forbidden content and automatically receive detailed adjustable reports containing information about content types, its owners and disk volume used by them. File services help to save internet traffic – having been downloaded once from global network information is provided to other clients of IT-infrastructure from local network folders. Thus all subsequent downloads are quicker than the first one.
Perhaps Print service is the most appropriate way to manage printing process in the company. You will have possibility to create dedicated print-server that will allow you to manage document workflow distributing documents to different printing devices according to content importance and devices location as well as manage user rights concerning printing documents. The service helps optimizing printing speed creating virtual print queue according to documents priority. Using Print Service together with Active Directory will allow you to publish printers and manage print-server centrally by the means of group policies and provide users with quick searching printers by various parameters such as printer location in the building, printer department binding, etc.
To guarantee stable work of all Unified Underlying IT-infrastructure services updating of operating systems and related software is required. Updates resolve vulnerabilities found in the operating system and its services as well as optimize OS functionality making work of the whole IT-infrastructure faster. Windows Server Update Service (WSUS) is the best free tool that enables centralized managing updates of operating systems, office applications, Anti Viruses and other software on workstations and servers at your company. If you use WSUS to update your software you can be sure of the security because all updates are distributed directly from Microsoft company and do not contain malicious code. Besides using WSUS you save internet traffic because the updates are distributed from the dedicated server (virtual or physical) located inside your IT-infrastructure instead of remote server located in the internet network.
Current trends in the industry of information technologies highlight the necessity to convert physical server infrastructure to virtual environments.
According to Forbes investigation contemporary solutions based on virtualization technology can reduce capital (up to 50 per cent) and operating (up to 60 per cent) expenditures due to consolidating servers in virtual environment and decreasing the necessity of frequent hardware upgrade.
Furthermore applying virtualization technologies gives other advantages:
- Increasing energy efficiency of server hardware.
- Providing continuity of business-processes owing to high fault tolerance of virtualized environments.
- Reducing expenditures for administration due to high level of processes automation in managing virtual environment.
- Possibility of quick adjusting of virtualized environment following changing business requirements.
Implementing virtualization to IT-infrastructure at the stage of its creating will enable using other advantages of this technology in future:
- Workstations virtualization – transferring user workstations to virtual environment keeping workstation functionality and environment.
- Applications virtualization – application isolation to virtual “shell”, separated from operating system to resolve compatibility problems or test applications during their development.
Implementation of this solution includes following stages:
- IT-infrastructure design taking into account requirements of business-applications, fault tolerance level and available communications.
- Required solution components selection based on information about the potential of IT-infrastructure growth and new products implementation.
- Installing and configuring required solution components.
- Auditing existing IT-infrastructure (optional stage).
- Migration of the existing objects (user accounts of workgroups, email accounts of different mail systems, etc.) to the Unified IT-infrastructure of company.
- Testing solution components.
If you choose this solution as the first step to creating unified IT-infrastructure, you give to your business possibility to grow and develop using currently leading technologies and software products.
